The Power of the Human Firewall: Your First Line of Defense

In the digital age, where cybersecurity threats are evolving at an unprecedented pace, protecting digital assets has become a paramount concern for individuals and organizations alike. Beyond the layers of sophisticated technology designed to safeguard against cyber threats, there's a critical component that often gets overlooked: the human element. This brings us to the concept of the "Human Firewall" – an essential aspect of cybersecurity that combines the strength of human vigilance with technological defenses to create a comprehensive security posture.

Human Firewall Meaning
Human Firewall refers to the concept of empowering individuals within an organization to act as a layer of security defense against cyber threats. It involves training and educating employees on recognizing and responding to potential security breaches, phishing attempts, and other malicious activities. By fostering a culture of awareness and vigilance, employees can identify suspicious behavior, understand the importance of following security protocols, and effectively protect sensitive information. The human firewall complements technical security measures by addressing the human element of cybersecurity, acknowledging that informed and cautious users can significantly reduce the risk of cyber attacks.
Human Cyber Risk

The human element in cybersecurity represents both a vulnerability and a line of defense. Human error, such as falling for phishing scams, using weak passwords, or inadvertently downloading malware, can lead to significant security breaches. These incidents underline the importance of educating and training individuals to act as a robust first line of defense against cyber threats.
More importantly, Insider threats represent a substantial risk within the cybersecurity landscape, highlighting the complexity of maintaining organizational security. These threats are not always the result of mal-intentioned actions by employees; more often, they stem from a lack of awareness about the potential security breaches that can arise from seemingly harmless actions.
Importance of Human Firewall in Cybersecurity
The concept of a human firewall transcends beyond just an individual's capacity to prevent cyber threats; it embodies an organization-wide culture of security awareness. With cybercriminals increasingly exploiting human psychology rather than system vulnerabilities, the role of human vigilance has never been more critical.
In an era where cybercriminals skillfully exploit human psychology alongside technological vulnerabilities, emphasizing human vigilance becomes paramount. It is this comprehensive approach to cybersecurity, blending awareness, education, and proactive behavior, that equips organizations to effectively manage both insider threats and external cyber attacks, thereby safeguarding their data, reputation, and overall security posture.
Understanding Human Firewall
Human Vulnerability in Cybersecurity
Humans are often the weakest link in the security chain, susceptible to various forms of social engineering attacks that manipulate psychological weaknesses.
Role of Human Firewall as the First Line of Defense
A well-informed individual can identify, avoid, and report attempts to breach security, acting as a critical barrier to cyber threats.
Impact of Human Error on Cybersecurity
Human errors, such as misconfigured settings or the mishandling of data, can inadvertently provide cyber attackers access to secured systems, emphasizing the need for a strong human firewall.
Areas of Weaknesses to the Human Firewall
The human firewall, crucial in defending against cyber threats, often suffers from vulnerabilities that can significantly undermine its effectiveness. Understanding these areas of weakness is essential for strengthening cybersecurity measures and ensuring that individuals and organizations are better equipped to protect themselves. Here's a detailed exploration of each vulnerability:
Phishing Attacks
Phishing attacks are a common and effective tactic cybercriminals use to deceive individuals into disclosing sensitive information, such as login credentials and financial data. These attacks typically involve sending fraudulent emails or messages that appear to be from legitimate sources, urging the recipient to click on malicious links or attachments. The success of phishing relies heavily on exploiting human psychology and the tendency to trust familiar-looking communications.
Malware

Malware, short for malicious software, encompasses various types of harmful software, including viruses, worms, trojan horses, and ransomware. Cybercriminals deploy malware to disrupt operations, steal sensitive data, or gain unauthorized access to systems. Humans often inadvertently facilitate malware infections by downloading infected files, clicking on malicious links, or using compromised USB drives.
Pretexting
Pretexting involves the creation of a fabricated scenario (or pretext) by attackers to obtain personal, financial, or security information. Unlike phishing, which relies on urgency or fear, pretexting builds a false sense of trust between the attacker and the victim. Attackers might impersonate co-workers, police, bank officials, or other persons of authority to extract confidential information.
Phone Scams
Phone scams, or vishing (voice phishing), use social engineering over phone calls to trick individuals into divulging personal information or making financial transactions. Attackers might pose as representatives from trusted organizations, claiming issues that require immediate attention, such as problems with a bank account or computer.
Baiting
Baiting exploits human curiosity or greed, offering something enticing to lure victims into a trap that could compromise their security. This could be as simple as a flash drive labeled "Confidential" left in a public place or digital downloads promising free access to software, movies, or music, which, when accessed or opened, lead to malware infections.
Quid Pro Quo
Quid pro quo attacks promise a benefit in exchange for information. This could involve an attacker offering free IT assistance in return for login credentials or other sensitive information. Victims are tricked into believing they are receiving something of value when, in reality, they are being manipulated into compromising security.
Tailgating
Tailgating, or piggybacking, involves an unauthorized person following an authorized individual into a restricted area or system without their knowledge. In physical security, this might mean literally following someone through a secured entry. In digital terms, it can refer to unauthorized access gained by exploiting legitimate users' credentials or sessions.
Theft/Loss of Company Devices

The theft or loss of company devices such as laptops, smartphones, and tablets poses a significant risk. These devices often contain sensitive information and, if not adequately protected, can provide easy access to unauthorized users. This vulnerability underscores the importance of physical security measures and encryption in safeguarding data.
Password Sharing
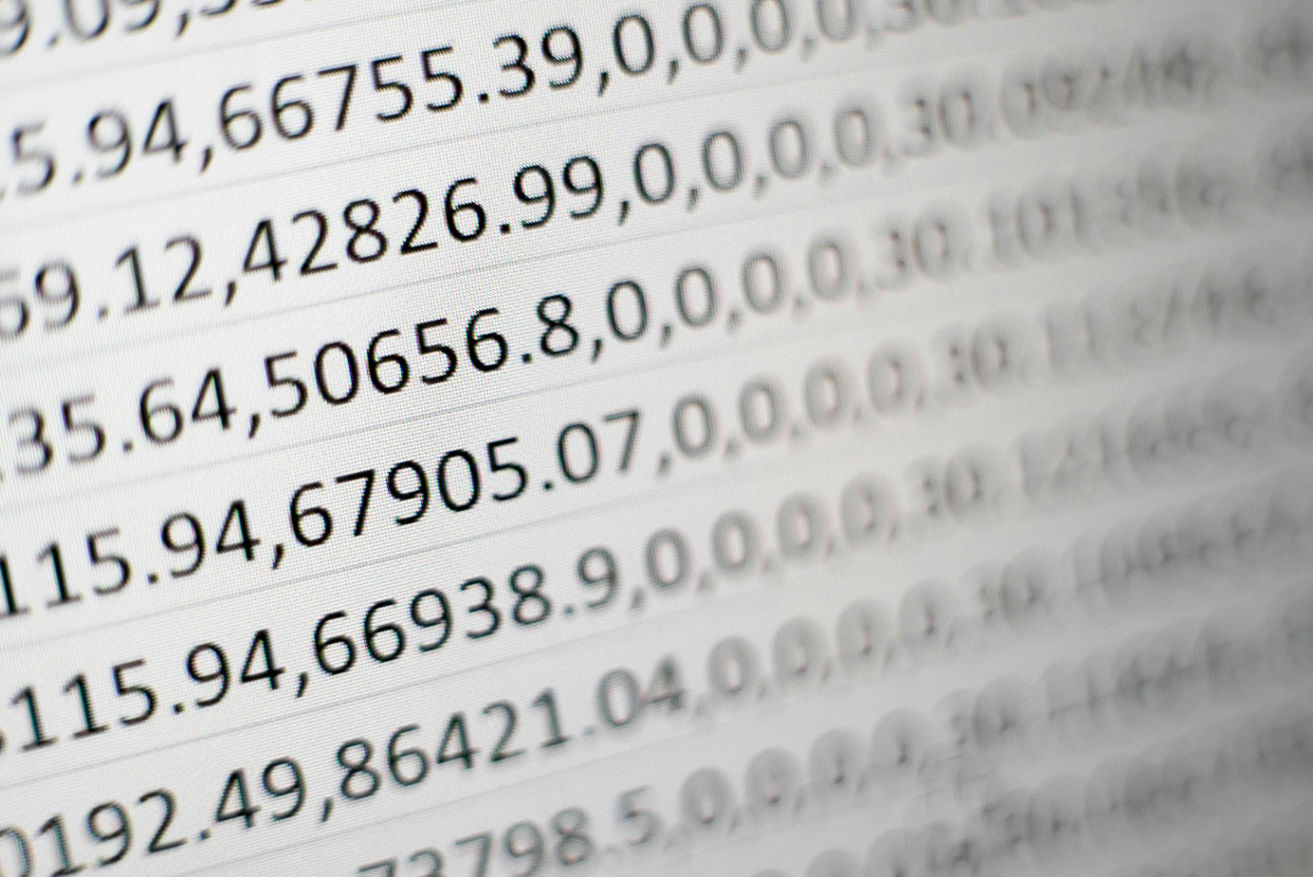
Password sharing, the practice of using the same credentials across multiple accounts or sharing them with others, significantly weakens security. It increases the risk of unauthorized access, as a breach in one account can lead to a domino effect, compromising multiple accounts and systems.
Accessing Sensitive Information in Public
Accessing sensitive information over unsecured public Wi-Fi networks or in view of prying eyes can lead to data breaches. Public networks are notoriously insecure, offering cybercriminals a prime opportunity to intercept data. Similarly, viewing confidential information in public places risks exposing it to shoulder surfing.
Lack of Training or Awareness
Perhaps the most significant vulnerability to the human firewall is the lack of cybersecurity training and awareness. Without an understanding of potential threats and safe practices, individuals are far more likely to fall victim to cyber-attacks. Regular, comprehensive training that keeps pace with evolving cyber threats is crucial to fortifying the human element of cybersecurity.
Addressing these vulnerabilities requires a multifaceted approach that includes ongoing education, robust security policies, and the use of technology to mitigate risks. By understanding and reinforcing these weak points, organizations can significantly enhance their human firewall, creating a more resilient defense against cyber threats.
How to Build and Strengthen a Human Firewall
Building and strengthening a human firewall involves a comprehensive approach that combines culture, training, policy, and technology. This multi-layered strategy ensures that every member of an organization is equipped with the knowledge and tools needed to defend against cyber threats effectively. Let's explore how to cultivate a robust human firewall within an organization.
Create a Culture of Cybersecurity Awareness Within the Organization
Cultivating a culture of cybersecurity awareness is foundational to building a strong human firewall. This involves integrating cybersecurity into the organizational ethos, making it a part of every employee's daily routine. Leaders should champion cybersecurity initiatives, demonstrating their importance through regular communication, support for training programs, and adherence to security policies. An environment where security is valued encourages proactive behavior and vigilance among all team members.
Design Cybersecurity Training to the Organization's Needs
Customized cybersecurity training tailored to the specific needs and vulnerabilities of an organization is crucial. Training programs should address the unique threats faced by the organization and equip employees with practical skills to recognize and respond to those threats. Regular training sessions, including new hire orientations, annual refreshers, and updates on emerging threats, ensure all employees know the latest security practices and protocols.

Human Firewall Techniques
Effective human firewall techniques involve a combination of behavioral adjustments, procedural changes, and technological solutions. These techniques include practicing good password hygiene, identifying and reporting suspicious activities, and adhering to the organization's security policies. Encouraging employees to think critically about the emails they open and the attachments they download can significantly reduce the risk of successful phishing attacks and malware infections.
MFA or 2FA for Human Firewall
Implementing Multi-Factor Authentication (MFA) or Two-Factor Authentication (2FA) significantly enhances security by adding an extra layer of defense beyond just passwords. By requiring a second form of verification, such as a code sent to a mobile device or a fingerprint scan, MFA and 2FA make it much harder for attackers to gain unauthorized access to systems and data.
Dedicated Devices Issued by the Company
Providing employees with dedicated work devices helps control the security environment and reduces the risk of cross-contamination from personal devices. These devices can be equipped with security software, configured with appropriate settings, and monitored for compliance with organizational security policies.
Recognizing and Preventing Phishing Attacks
Training employees to recognize and respond appropriately to phishing attempts is a key component of a strong human firewall. This includes identifying suspicious email addresses, scrutinizing links and attachments, and verifying requests for sensitive information through alternative communication channels.
Test Your Employees with Phishing Tests
Regularly testing employees with simulated phishing emails and other security drills can assess their readiness to identify and avoid real threats. These tests help reinforce training, highlight areas for improvement, and ensure that security awareness remains high.
Phishing tests, as a part of the testing regime, specifically target the employees' ability to discern legitimate communications from phishing attempts. Analyzing the results of these tests can provide valuable insights into training effectiveness and employee vulnerabilities.
Continuous Improvement and Updates to System Security

Cybersecurity is an ever-evolving field, and so, too, must be the organization's approach to it. Regularly updating systems, software, and security protocols in response to new threats ensures that technological defenses and employee training remain current and effective.
Implementing Open-Door Policies for Reporting Security Risks
Creating an environment where employees feel comfortable reporting security concerns without fear of retribution is essential for the early detection of potential threats. An open-door policy encourages employees to speak up about suspicious activities, lost devices, or any security lapses they may encounter.
Understanding Social Engineering Techniques
Educating employees about social engineering tactics, including how attackers exploit human psychology to gain trust and extract information, prepares them to better recognize and resist these attempts.
Utilizing Security Technology to Augment the Human Firewall
Leveraging advanced security technologies, such as threat detection systems, encryption tools, and secure communication platforms, provides a safety net that complements the human element of cybersecurity.
Penalties for Repeat Employee Offenders
While fostering an understanding and supportive environment is key, it may also be necessary to implement penalties for repeat offenders who consistently violate security policies. These measures should be designed to reinforce the seriousness of cybersecurity and encourage compliance. More about this can be read in this LinkedIn Post by Bill Murphy.
Is a Human Firewall Helpful on an Individual Level or a Business?
Absolutely. On an individual level, it empowers people to protect their personal information and digital footprint. For businesses, it creates a vigilant workforce capable of identifying and mitigating cybersecurity threats, thereby protecting the organization's data and reputation.
Conclusion
The human firewall is a critical component of any comprehensive cybersecurity strategy. By fostering a culture of awareness, providing targeted training, and leveraging technology, individuals and organizations can significantly reduce their vulnerability to cyber threats. As cybercriminals become more sophisticated, the human firewall will continue to play an indispensable role in safeguarding digital assets.
For further insights into enhancing your cybersecurity posture and exploring advanced security solutions, visit our Virtual Security Operations, RedZone Products, and Resources pages. As the digital landscape evolves, so too must our defenses. Strengthening the human firewall is not just a task for IT departments but a shared responsibility that requires active participation from all stakeholders. Let's work together to build a safer digital world. Ready to take your cybersecurity to the next level? Contact us today.

FAQs
How does the concept of "digital hygiene" relate to maintaining a robust human firewall?
Digital hygiene involves practices like updating software, using strong passwords, and being cautious with online activities. These habits contribute to a robust human firewall by reducing vulnerabilities that attackers exploit. Just as personal hygiene prevents illness, digital hygiene prevents cyber threats, reinforcing the overall security posture of individuals and organizations.
Are there specific industries or sectors that are more vulnerable to breaches despite having a human firewall in place?
Certain industries, like healthcare and finance, often handle sensitive data, making them prime targets for cyberattacks despite robust human firewalls. Their attractiveness to attackers, coupled with complex regulatory requirements, can create vulnerabilities that require constant vigilance and adaptation of security measures to mitigate risks effectively.
How does the concept of zero-trust security intersect with the role of the human firewall?
Zero-trust security rejects the notion of implicit trust within networks, requiring verification for every access attempt. This aligns with the human firewall concept, emphasizing skepticism towards all requests for access or information. It underscores the importance of continuous authentication and authorization, enhancing overall security against internal and external threats.
Are there any emerging technologies or trends that are reshaping the effectiveness of human firewalls in cybersecurity?
Emerging technologies like artificial intelligence and machine learning are reshaping human firewalls by enabling proactive threat detection and response. Additionally, advancements in user behavior analytics help identify anomalous activities, strengthening defenses against insider threats. Moreover, the rise of remote work has spurred innovations in secure collaboration tools and endpoint protection, adapting human firewalls to evolving cybersecurity landscapes.
 Security Updates
Security UpdatesUnderstanding IT Compliance: Scope, Benefits, and Challenges
Discover what IT compliance is, its importance, benefits, risks of non-compliance, frameworks, and how to achieve robust IT compliance in your organization.
 Security Updates
Security UpdatesImplement Secure Browsing with Powerful SSL Decryption
Explore the essentials of SSL decryption, its importance, challenges, and best practices for enhancing security and compliance for business in a detailed guide
 Security Updates
Security UpdatesTransitioning from Proxy Firewalls to Endpoint Security
Explore the evolution from proxy firewalls to endpoint security, enhanced threat detection, data encryption, and comprehensive protection for modern networks.
 Security Updates
Security UpdatesExpert IT Risk Assessment: Protect Your Business Today!
Mitigate potential IT threats with our comprehensive risk assessment guide, ensuring your digital infrastructure. Ensure your business is secure an...
 Security Updates
Security UpdatesEssential Guide to Best Practices in Compliance Security
Explore essential strategies for compliance security in this comprehensive guide. Learn about safeguarding your business and meeting regulatory sta...
 Security Updates
Security UpdatesSecure Your Data with Expert Cloud Database Solutions
Learn efficient solutions and secure your cloud databases with encryption and compliance features, ensuring data safety and privacy across all plat...
 Security Updates
Security UpdatesA Guide to Cloud Network Technology: Benefits and Types
Unlock the potential of cloud network technology for seamless connectivity. Learn and scale solutions that drive business innovation and growth via...
 Security Updates
Security UpdatesAffordable Managed IT Services for Small Businesses
Explore top-managed IT services for small businesses to boost efficiency and security. Get expert insights and practical tips to optimize your IT o...
 Security Updates
Security UpdatesSecure Your Network with Gateway Security Solutions
Explore the essentials of gateway security: learn about its importance for network protection and best practices to safeguard your digital assets e...
 Security Updates
Security UpdatesDisaster Recovery Testing: Ensure Business Continuity
Explore effective disaster recovery testing strategies in this guide to maintain business continuity, prevent data loss, and minimize downtime duri...
 Security Updates
Security UpdatesMaximizing Security: Vulnerability Management Lifecycle
Explore the complete guide to the Vulnerability Management Lifecycle to boost your cyber resilience and secure your business IT infrastructure effe...
 Security Updates
Security UpdatesYour Network with Endpoint Security Management
Explore our comprehensive guide on Endpoint Security Management to understand its importance, how it works, and best practices for robust network s...
 Security Updates
Security UpdatesEnsuring Security Compliance: Tips, Insights & Strategies
Discover the essentials of security compliance, its importance, frameworks, and tools. Learn how to protect data and meet regulatory standards effe...
 Security Updates
Security UpdatesBoost Your Security with Internal Penetration Testing
Dive into internal penetration testing with our in-depth guide. Learn the essentials, techniques, and best practices to fortify your cybersecurity ...
 Security Updates
Security UpdatesEgress vs Ingress: A Guide to Data Traffic Management
Understand Egress vs Ingress in data management. Learn and explore their roles, traffic analysis, risks, and best practices for network and cloud s...
 Security Updates
Security UpdatesPrevent Credential Harvesting to Protect Your Precious Data
Understand credential harvesting. Learn how it works, common techniques, its impact, and strategies to prevent and mitigate attacks to secure your ...
 Security Updates
Security UpdatesSecure Your Big Data: Top Solutions for Data Security
Protect your valuable data with our robust big data security solutions. Learn about the threats and Safeguard against cyber threats and ensure comp...
 Security Updates
Security UpdatesSecure Your Network with Advanced Management Solutions
Explore the details of comprehensive network security management: Learn key strategies, best practices, and tools to safeguard your digital environ...
 Security Updates
Security UpdatesGuide to On-Path Attacks: Protecting Your Cybersecurity
Learn about on-path attacks in this comprehensive guide, exploring definitions, types, consequences, and key prevention strategies to safeguard you...
 Security Updates
Security UpdatesExploring Managed Cloud Services: A Comprehensive Guide
Dive into the Managed Cloud Services with our in-depth guide. Explore benefits, types, and best practices to enhance your business's cloud strategy...
 Security Updates
Security UpdatesComprehensive Guide to Ubiquitous Computing: Impact & Future
Explore the details of ubiquitous computing, from its core concepts and layers to its societal impact, key technologies, applications, and future p...
 Security Updates
Security UpdatesClone Phishing Explained: Detection and Prevention Guide
Discover how clone phishing works and its impact. Learn effective strategies to identify, prevent, and respond to these sophisticated email threats...
 Security Updates
Security UpdatesHow to Secure Your Business with Cyber Security Insurance
Explore the essentials of Cyber Security Insurance, covering its importance, types of coverage, benefits, and considerations for businesses in the ...
 Security Updates
Security UpdatesEfficient Data Spooling Solutions For Streamlined Operation
Learn How To Efficiently Manage And Store Your Data With Our Reliable Data Spooling Services. Keep Your Information Organized And Accessible With T...
 Security Updates
Security UpdatesMaximizing Compliance & Risk Management: Expert Strategies
Learn how to ensure business success with effective compliance and risk management strategies. Explore definitions, differences, frameworks, and ch...
 Security Updates
Security UpdatesUnderstanding MDF vs IDF: Key Differences & Benefits
Explore the crucial differences and examples between MDF and IDF in networking, understanding their roles, functions, and impact on network infrast...
 Security Updates
Security UpdatesRedZone Wins CRN's Top Security 100 & MSP 500 Awards 2024
RedZone Technologies earns CRN's Security 100 & MSP 500 Awards, affirming its leadership and innovative approach in the cybersecurity and IT manage...
 Security Updates
Security UpdatesJames Crifasi Speaks on Cybersecurity at Tech Conference
Join James Crifasi, CTO & COO of RedZone Technologies, at the Tech Conference as he explores cybersecurity's role in driving business growth and ad...
 Security Updates
Security UpdatesRedZone's James Crifasi Wins SonicWall's Technical Hero Award
CTO James Crifasi of RedZone Technologies earns SonicWall's Technical Hero of the Year, exemplifying unparalleled dedication to cybersecurity and I...
 Security Updates
Security UpdatesHow to Encrypt Email in Outlook
Learn how to encrypt email in Outlook with our step-by-step guide. Secure your messages using S/MIME, Office 365 Encryption OME, and add-ins for pr...
 Security Updates
Security UpdatesWhat Is Security Monitoring? Importance and Tools
Explore the importance of security monitoring, its key roles, types, and how it protects organizations against threats, ensuring compliance and pro...
 Security Updates
Security UpdatesServer 2012 R2 End of Life: Implications and Next Steps
Learn about Server 2012 R2 end of life: Understand its impact, key dates, risks post-EOL, and explore upgrade options and migration strategies for ...
 Security Updates
Security UpdatesProtect Personal Data: Smishing and Phishing Prevention
Know how to identify and protect against smishing and phishing attacks. Learn the techniques, types, and preventive measures for personal and busin...
 Security Updates
Security UpdatesSmurf Attack Guide: Prevention & Detection Strategies
Explore prevention & recovery from Smurf Attacks: Understand DDoS defense, detection signs, and secure network practices in our detailed cybersecur...
 Security Updates
Security UpdatesWhat is a Bad USB Attack, and How Do You Prevent It?
Learn about Bad USB attacks, their various forms, and strategies for safeguarding devices. Learn how to mitigate risks with effective prevention te...
 Security Updates
Security UpdatesKey Differences Between DOS Attack vs DDOS Attack
Explore the key differences between DDoS vs DoS attacks, their types, impacts, and prevention strategies in our comprehensive guide to enhance cybe...
 Security Updates
Security UpdatesUnderstanding the Impact of a Ping of Death Attack
Explore the ins and outs of Ping of Death attacks. Understand how they work, their impact on networks, and strategies to prevent them to keep your ...
 Security Updates
Security UpdatesThe Power of the Human Firewall: Your First Line of Defense
Discover the critical role of the human firewall in cybersecurity, combining employee vigilance with technology to protect against cyber threats ef...
 Security Updates
Security UpdatesStateful Firewall vs. Stateless Firewalls: What's the Difference?
Learn the key differences between stateful and stateless firewalls and how they protect your network. Discover the right choice for your security n...
 Security Updates
Security UpdatesUnderstanding the 4 Levels of PCI Compliance
Explore PCI DSS Compliance with RedZone: Key steps to protect card data and ensure secure transactions. Learn about compliance levels and tips for ...
 Security Updates
Security UpdatesWhat Is a Security Breach and How to Prevent Them
Learn how to effectively guard your business against security breaches with RedZone Technologies. Discover simple steps to keep your data safe and ...
 Security Updates
Security UpdatesUnderstanding Tailgating in Cybersecurity
Understand tailgating attacks in cybersecurity: what they are, how they work, and effective strategies for prevention to keep your business...
 Security Updates
Security UpdatesWhat is a Managed Service Provider and Its Benefits
Explore the role of Managed Service Providers (MSPs) in enhancing IT efficiency and cybersecurity for businesses, covering benefits, servi...
 Security Updates
Security UpdatesBreach Prevention: 5 Best Practices to Protect Your Data
Learn about data breaches: what they are, their impact, and how to prevent them. Explore best practices for securing your business against cyber th...






